Amazon Virtual Private Cloud (Amazon VPC) is one of the major offerings of Amazon Web Services (AWS) that allow users to define a logically isolated virtual private network to provision AWS resources. The virtual private network resembles a traditional network that is used by customers in their own data centers along with the additional benefits of the scalable infrastructure of the AWS cloud.
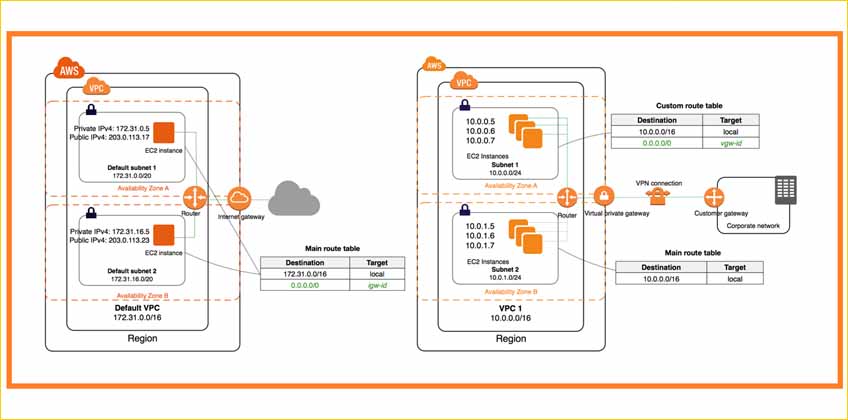
The components of VPC include IP addresses, subnets, network interface, gateways, endpoints, route tables, and more. Although Amazon Web Services has built strong security to a certain extent into its VPC, still it is always recommended to ensure the hosted data, servers and applications as an AWS administrator.
This article focus on such 5 tips that helps users make the VPC and the resources reasonably secure.
What is Amazon Virtual Private Cloud
The private cloud environment has become a popular choice for businesses that are searching for a cloud communications solution yet don’t want to use pooled cloud resources. Public cloud systems are off-limits due to the risk that they may be sharing data with other businesses, possibly even their competitors. This is where the Amazon Virtual Private Cloud infrastructure comes to the rescue. By provisioning a logically isolated area of Amazon Web Services Cloud, the Amazon Virtual Cloud gives consumers access to a virtual private cloud. Enterprise clients can use an IPsec-based virtual private network to access the Amazon Elastic Compute Cloud. With the help of Amazon private cloud, you can start launching AWS resources into a defined virtual network. This virtual network has the advantage of using the scalable infrastructure of AWS, while closely resembling a conventional network that you would operate in your own data center.
How does Amazon Virtual Private Cloud work?
Amazon’s virtual private server brings the best features of private and public cloud systems together. When running on a public or shared architecture, VPCs perform like a private cloud. Amazon VPC is most frequently utilized in the context of cloud “infrastructure as a service” (IaaS), where Amazon provides the infrastructure for organizations to operate on. In Amazon’s virtual private cloud setup, each customer’s data is kept separate from every other customers while it is being transferred and stored on the cloud provider’s network. The following security policies are deployed by Amazon to ensure the utmost security for customer data:
- Encryption: Virtual private networks, or VPNs, layer a private network over a public network using encryption. The internet infrastructure via which VPN traffic travels includes publicly accessible routers, switches, etc. However, because the traffic is jumbled, it is invisible to other users.
- Private IP addresses or subnets: An IP address range in a network that is set aside for a certain user is known as a subnet. Unlike regular IP addresses, these private IPs cannot be accessed via the public internet.
- Allocation of virtual local area network (VLAN) for each customer: A VLAN is a collection of computing devices linked together directly over the local area network (LAN). Similar to a subnet, a VLAN can divide a network; however, this division happens at layer two as opposed to layer 3 of the Open Systems Interconnection Model (OSI).
Suggested reading – Top 6 Security Strategies for Amazon Web Services in a Zero Trust World
Best security practices of Amazon Virtual Private Cloud
Here are some of the best security practices for using Amazon’s cloud hosted servers. It is worth noting that the following recommendations are only broad recommendations and not an entire security program. The best way to improve your infrastructure security is to treat these practices as security ideas instead of absolute directives because they might not be suitable or sufficient for your business context.
- Create your subnets in various Availability Zones as you add them to your VPC to host your application. One or more separate data centers with redundant power, networking, and connectivity make up an availability zone in an AWS region. Your production applications become highly available, fault-tolerant, and scalable when you use several Availability Zones.
- Use security groups to manage traffic to EC2 instances in your subnets and network ACLs to manage access to your subnets.
- Utilize AWS Identity and Access Management (IAM) identity federation, users, and roles to control access to AWS VPC resources and APIs.
- Use Amazon CloudWatch with VPC flow logs to keep an eye on the IP traffic entering and leaving your VPC.
5 Tips to Boost Security of Amazon Virtual Private Cloud
#1 Start working with a detailed plan: Planning before creating a new virtual private cloud help users outline its design and functionality. The most important factor considered while planning out the working of VPC is to identify its purpose. Will it be used to host a user- interactive website or to extend the on-premises corporate network of the enterprise in the AWS cloud? Predicting the groups of user applications and services that will access the VPC after creation is equally important. Another important factor is to consider the type of connectivity required between the VPC and other internal and external networks belonging to the organization, partners, or customers. Knowing the need for VPC required to create additional virtual connections that ensure connectivity with resources in other regions is very important. So, including these ideas in the detailed plan ensures uptight security of your cloud.
#2 Creating a new Virtual Private Cloud: Although, AWS offer users with a default Virtual Private cloud in each region of their AWS account, it’s recommended to create a new VPC instead using the default one. The prime reason to create own VPC is that the security configuration of the default VPC is usually wide open as the subnets in the default VPC are associated with the main routing table which does not put any restrictions on the inbound and outbound traffic. Therefore to secure the private cloud connection and the AWS resources, one must always consider opting a new virtual private cloud and define its custom route further. This practice ensures the total security of the AWS environment
#3 Create multiple VPCs if required: Creating a mirror VPC of the original one, to host the applications, servers, and data doubles up the security measures of the AWS cloud. Also, one of them can be used for production and the other for development. It is highly recommended to keep the testing and production environment separately so as to make the development model more robust and agile.
#4 Using Security Groups: Security groups are usually virtual firewalls that filter the type of traffic entering and leaving the VPC. These security groups are always permissive, without any deny rules. So when the user creates the security groups for a newly created VPS, it automatically allows unrestricted outbound traffic, and no inbound traffic, which is an obvious secure configuration. Additionally, various cloud experts recommend using security groups instead of Network Access control Lists (NACL), which again are another form of virtual firewall that controls the incoming and outgoing flow of traffic. The reason behind restricting the use of NACLs is because when the users create a new NACL it does not allow any type of traffic, be it inbound or outbound, to flow. So the basic difference between the security group and NACLs are that the former can be more granularly used than the latter as it controls network traffic in a much ideal way.
Suggested reading – Know these 5 contemporary offerings from Amazon Cloud Services
#5 Using Elastic IP Addresses: The last, but an important tip to boost the AWS public cloud environment is making use of elastic IP addresses. If the resources hosted in the VPC requires connectivity to the Internet so that the users and applications can access them, then the network admin preferably has a choice of how they can make this connectivity happen. Either a public IP address to any instance or the network interface can be assigned in the VPC, or an Elastic IP Address (EIP) can be used for such purposes. The main reason behind using the EIP is its availability. So, if your instance fails for some reason, the associated public IP address shuts down and is lost automatically. However, using an EIP can save the IP address by moving it to some other instance. Hence, EIP is one of the most useful and promising security considerations for VPC architecture.
There still exist some other practices apart from the aforementioned ones that can be adopted to ensure the security of the AWS-hosted servers, applications, and data.
If you wish to host web applications with multiple layers of privacy and security afforded by Amazon Virtual Private Cloud and are looking out for an AWS cloud partner provider, you can totally rely on the cloud services and offerings of i2k2 Networks, with a business continuity record from over 20-years in the cloud computing market. We help you extend your corporate network in the cloud to host multi-tier web applications and make your resources scalable with greater availability, connectivity, and flexibility at such affordable prices. Avail our lucrative cloud resources by connecting on +91-120-466-3031 | +91-971-177-4040 or at sales@i2k2.com. Or just fill this form to avail 7 Days Free Trial Offer on our web hosting services.